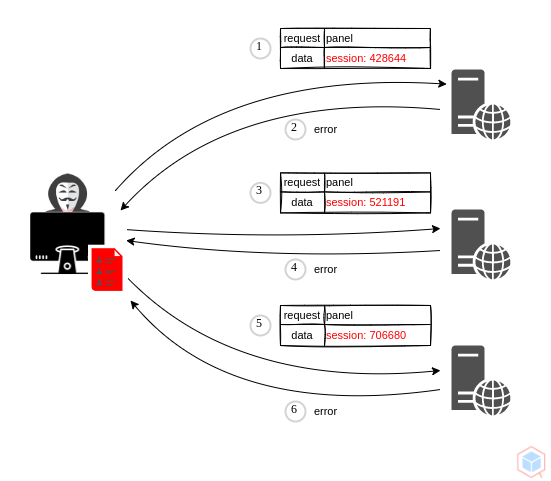
A threat actor may re-use a stolen or leaked session identifier to access the user's account.
- Threat actor obtains a valid session identifier and does not use it immediately
- Threat actor re-using the same session identifier to gain unauthorized access to a victim's account
- Bob submits a request to buy an item from a vulnerable website
- Threat actor finds the request and tricks bob into re-submitting it
- The vulnerable website receives both requests with the same session identifier and processes them
Vary
- gain unauthorized access
- Identity confirmation
- Regenerate session ids at authentication
- Timeout and replace old session ids
- Store ids in HTTP cookies
fe0561ad-6ce7-4cf3-a229-eb136ad1f919